Contact lenses from contactlenses.co.uk are perfect for those who want a dramatic change in eye color. And with the number of brands and options available, it’s confusing to decide which one to choose. Bella colored contact lens and anesthesia lens are among the few popular brands that offer an amazing range of unique lens and a wide…
Have you ever felt the need to check if a domain name is still available or the name or brand of the owner of a certain website because you want to connect with them? If so, you can do it by getting access to that information through domain lookup. You can easily find out what…
In today’s technological society, utilizing modern communication tools keeps you and your business abreast with modern trends. Writers are among those that can most benefit from the website conversion funnel. Generating and presenting quality content is the competition, such as ways on how to write a call to action and utilizing reputable sources are just…
The new technological age not only brought with it high-end automated systems, but also turned the virtual market around with the creation, nine years ago, of the first electronic currency: The Bitcoin. Yes, cryptocurrencies have totally transformed the economic system that the world used to have. At first the idea of investing large amounts of…
The general overview of the Microsoft Azure 70-532 certification exam covers core topics which are related to the knowledge of a developer that builds solutions of cloud-native for Azure. For 70-532 Developing Microsoft Azure Solutions exam, the students must understand the concepts of virtual machine deployment and configuration, must be able to choose from various…
Project management has gained great importance in companies. In addition to being a tool to develop products or services, projects are becoming a useful strategic way to survive in the current competitive environment. Software already exists and serves to create new services and products, whether for development projects, reorganization or any other type, their correct…
There is no doubt we are living in the mobile age and whether we love our smartphones or are one of those that think we spend too much time on them one thing is for sure and that is the spin-off industries have made a great deal of money from the portable computer that fits…
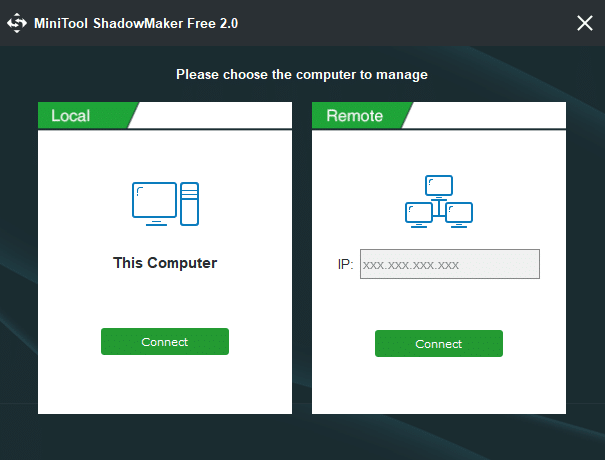
Overview of Windows System Backup What is Windows backup? When and why do you need to back up operating system? Window 10 backup is the process of back up operating system files and data. Operating system backup can ensure that the data of operating system is saved, and can save system state and operational condition….
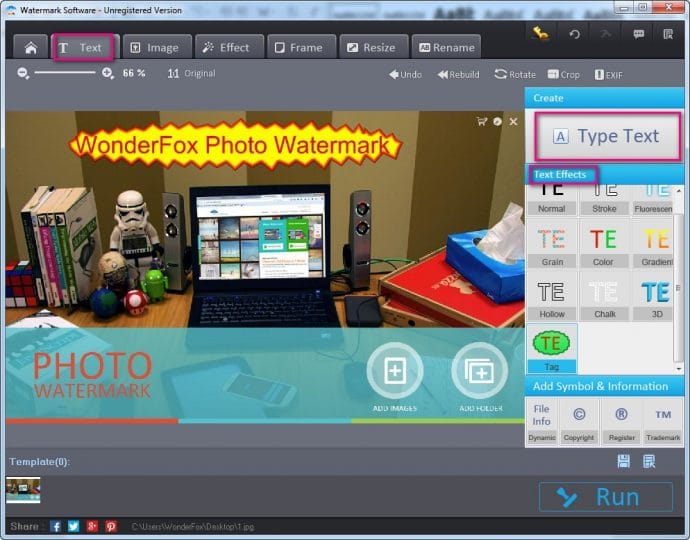
Are your own photos stolen by others? Are your own photos used in other sites by others without your permission? If you want to prevent this situation, what you can do is add watermark to your photos. WonderFox Photo Watermark is an easy-to-use software which can protect your pictures from being stolen or copied by…
Restoring your smart phone allows you to return it to optimal performance. Sometimes smartphones don’t function the way we expect, and the best way to troubleshoot a severe problem with your phone is to simply restore the device to a factory default or older version. It doesn’t matter if you’re restoring an Android or an…